Software
-
 271
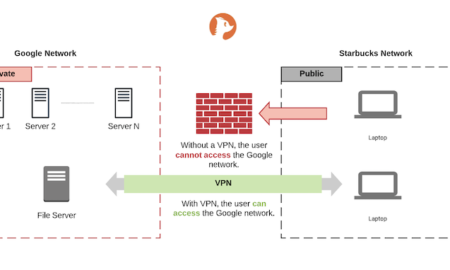
271Does VPN bypass DNS filtering?
Usually a VPN service first installs a VPN client, and for all future VPN traffic the path is fixed and encrypted –...
-
 185
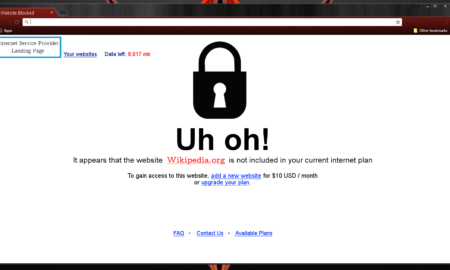
185Why are some websites blocked?
Internet service providers (ISPs) typically block websites for legitimate reasons — URLs known to contain or traffic illegal or pirated content are...
-
 184
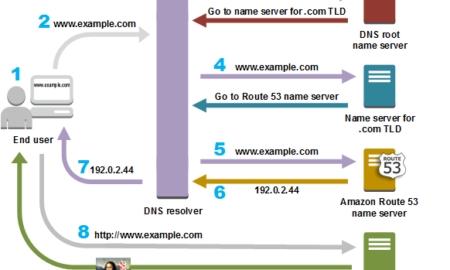
184Was macht das DNS?
Das DNS-System des Internets funktioniert ähnlich wie ein Telefonbuch: Es verwaltet die Zuweisung zwischen Namen und Nummern. DNS-Server übersetzen Namensanforderungen in IP-Adressen...
-
 237
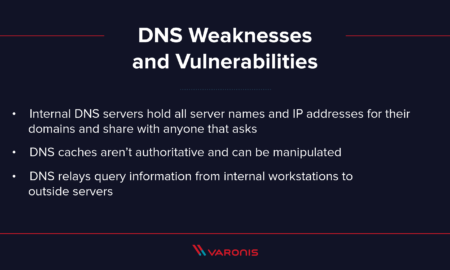
237What can someone do with my DNS?
DNS hijacking can be used for pharming (in this context, attackers typically display unwanted ads to generate revenue) or for phishing (displaying...
-
 215
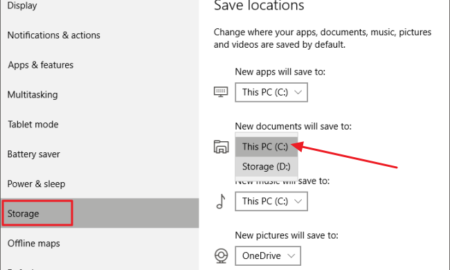
215Should I save files in C or D?
A modern way is to keep the OS and Apps on C to make it smaller for imaging purposes, User data folders...
-
 236
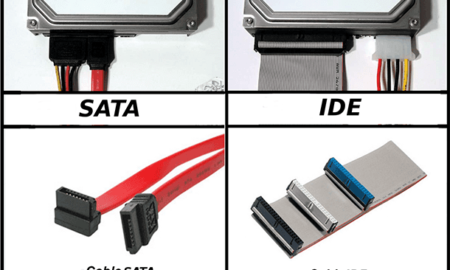
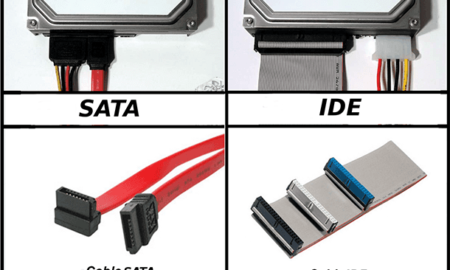
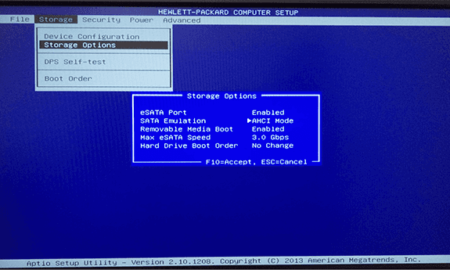
236How do I know if my SATA is in AHCI mode?
Check for an entry that contains the acronym “AHCI.” If an entry exists, and there is no yellow exclamation mark or red...
-
 277
277Does AHCI support SSD?
AHCI supports Windows, Linux, and UNIX operating systems. Note that SATA SSDs do not use AHCI, which is the software protocol between...
-
 249
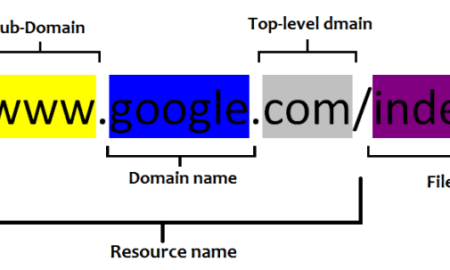
249Is a URL a DNS?
A domain name is used in conjunction with a domain name system, which includes the top-level domain, DNS caching, and an authoritative...
-
 193
193Is AHCI mode better?
Should SATA mode be AHCI or IDE? Generally speaking, IDE mode provides better compatibility for the older hardware. But the hard drive...
-
 223
223Should I keep old hard drives?
It is not necessary to keep an old drive. In fact, it’s most likely not even worth it. Along with the rest...










Recent Comments