Need
-
 261
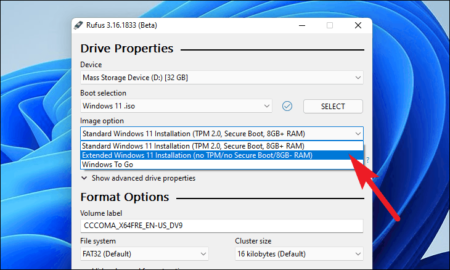
261Can Windows 11 install on Legacy BIOS?
You only need to prepare a USB falsh drive and Windows 11 installation ISO file, and then you can easily install Windows...
-
 175
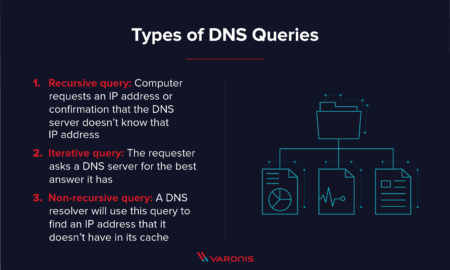
175What is DNS how it works give one advantage of it?
The Internet’s DNS system works much like a phone book by managing the mapping between names and numbers. DNS servers translate requests...
-
 269
269Does VPN block DNS?
A “Full-Tunnel” VPN routes and encrypts all the Internet traffic through the VPN. Consequently, DNS requests are also encrypted and out of...
-
 280
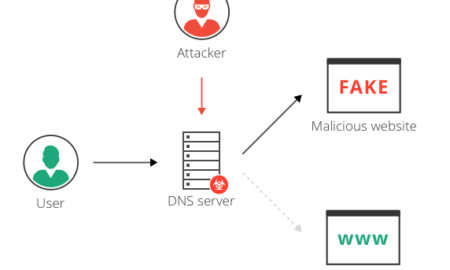
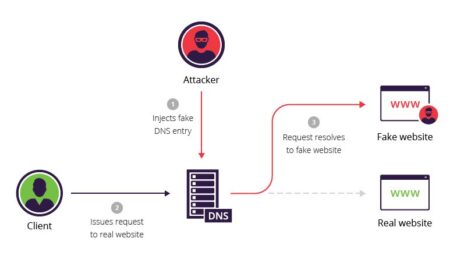
280How do hackers redirect traffic?
Local DNS hijack — attackers install Trojan malware on a user’s computer, and change the local DNS settings to redirect the user...
-

 286
286Can governments track VPN?
If you’re using a trustworthy VPN service, your browsing activities become illegible to snoopers. However, this doesn’t mean a VPN user is...
-

 195
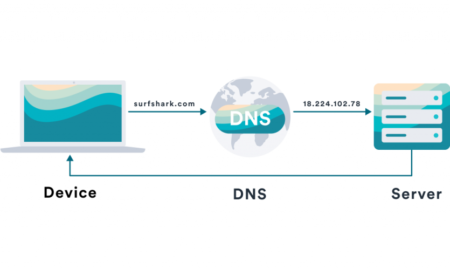
195What is DNS
BeschreibungDas Domain Name System, deutsch Domain-Namen-System, ist ein hierarchisch unterteiltes Bezeichnungssystem in einem meist IP-basierten Netz zur Beantwortung von Anfragen zu Domain-Namen....
-

 224
224What is safe boot in BIOS?
Secure Boot is one feature of the latest Unified Extensible Firmware Interface (UEFI) 2.3. 1 specification (Errata C). The feature defines an...
-

 287
287Can I change my BIOS from Legacy to UEFI?
Normally, you can find the Legacy/UEFI boot mode configuration under the Boot tab. Under the Boot tab, you should disable Legacy and...
-
 176
176What is an example of DNS spoofing?
What is spoofing attack example? Spoofing techniques vary based on the type of attack. For example, in email spoofing, the adversary can...
-
 195
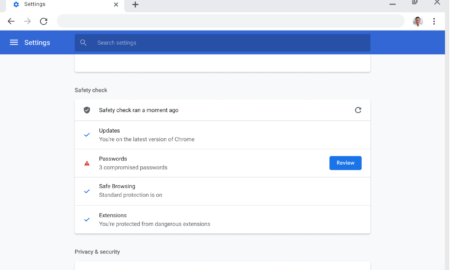
195Should I do a Chrome safety check?
Safety check helps ensure the overall security and privacy of your browsing experience. It will notify you if any passwords saved in...










Recent Comments